Despite the enormous amount of resources required to design them, small-cap cryptocurrencies are still susceptible to 51% of attacks.
Despite being backed by blockchain technology that promises security, immutability, and full transparency, many cryptocurrencies like Bitcoin SV BSV-$39.62, Litecoin Cash (LCC), and Ethereum Classic ETC-$19.45 have been subject to 51% attacks multiple times. in the past. While there are many mechanisms by which malicious entities can and have exploited blockchains, a 51% attack, or majority attack as it is also called, occurs when one group of miners or one entity controls more than 50%. of the hashing power of the blockchain and then assumes control over it.
Possibly the most expensive and tedious method of compromising a blockchain, 51% of attacks have been highly successful with smaller networks that require less hash power to traverse most nodes.
Understanding a 51% attack
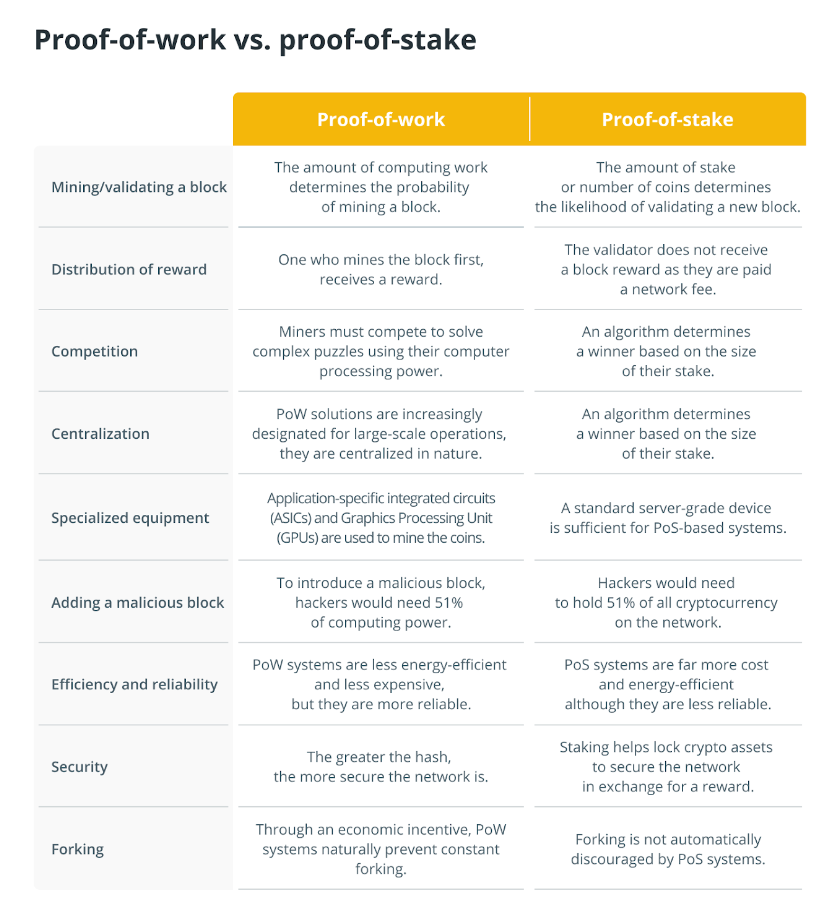
Before delving into the technique involved in a 51% attack, it is important to understand how blockchains record transactions, validate them, and the different controls built into their architecture to prevent any changes. Using cryptographic techniques to connect subsequent blocks, which are themselves records of transactions that have taken place on the network, a blockchain adopts one of two types of consensus mechanisms to validate each transaction in its network of nodes and permanently record them. .
While nodes on a proof-of-work (PoW) blockchain need to solve complex math puzzles to verify transactions and add them to the blockchain, a proof-of-stake (PoS) blockchain requires nodes to stake a certain amount of money. native token amount to get the state of the validator. Either way, a 51% attack can be orchestrated by controlling the network’s mining hash rate or by controlling more than 50% of the tokens staked on the blockchain.
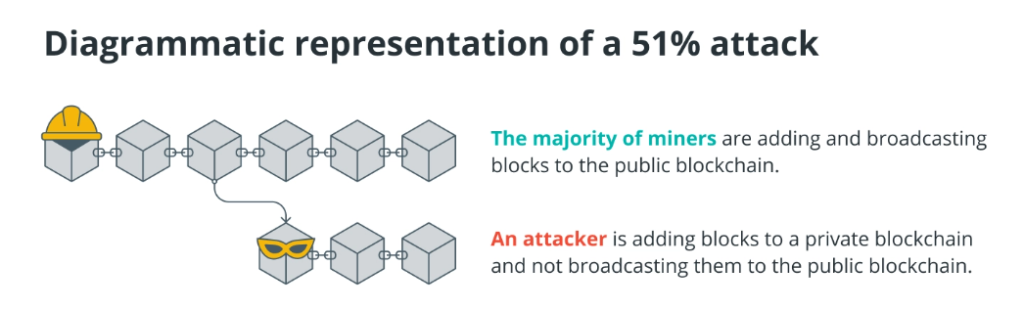
To understand how a 51% attack works, imagine if more than 50% of all nodes performing these validation functions conspire to introduce a different version of the blockchain or execute a denial of service (DOS) attack. The latter is a type of 51% attack in which the remaining nodes are prevented from performing their functions while the attacking nodes add new transactions to the blockchain or delete old ones. In either case, attackers could potentially reverse transactions and even spend double the native crypto token, which is akin to creating a counterfeit currency.
It goes without saying that such a 51% attack can compromise the entire network and indirectly cause huge losses to investors holding the native token. Although creating an altered version of the original blockchain requires an extraordinarily large amount of computing power or staked cryptocurrency in the case of large blockchains like Bitcoin or Ethereum, it’s not so far-fetched for smaller blockchains.
Even a DOS attack is capable of crippling the blockchain and can negatively affect the price of the underlying cryptocurrency. However, past transactions beyond a certain limit are unlikely to be able to be reversed and therefore only put the most recent or future transactions made on the network at risk.
Is a 51% attack on Bitcoin possible?
For a PoW blockchain, the probability of a 51% attack decreases as the hash power or computational power used per second for mining increases. In the case of the Bitcoin BTC-$16446 network, the perpetrators would need to control more than half of Bitcoin’s hash rate, which currently sits at ~290 exhashes/s of hash power, forcing them to gain access to at least 1.3 million of the most powerful application-specific integrated circuit (ASIC) miners like Bitmain’s Antminer S19 Pro, which retails for around $3,700 each.
This would imply that attackers would have to purchase mining equipment totaling around $10 billion just to have a chance of executing a 51% attack on the Bitcoin network. Then there are other aspects like electricity costs and the fact that they would not be entitled to any of the mining rewards applicable to honest nodes.
However, for smaller blockchains like Bitcoin SV, the scenario is quite different as the hash rate of the network is around 590 PH/s, making the Bitcoin network almost 500 times larger. . powerful than Bitcoin SV.
However, in the case of a PoS blockchain like Ethereum, malicious entities would need to have more than half of the total ETH-$1,163 Ether tokens that are locked up in network participation contracts. This would require billions of dollars just in terms of buying the computing power needed to even have the appearance of launching a successful 51% attack.
Furthermore, should the attack fail, all staked tokens could be confiscated or blocked, dealing a heavy financial blow to the entities involved in the alleged attack.
How to detect and prevent a 51% attack on a blockchain?
The first check of any blockchain would be to make sure that no one entity, mining pool, or even one mining pool controls more than 50% of the network’s mining hashrate or the total amount of tokens staked.
This requires blockchains to maintain constant control of the entities involved in the mining or staking process and take corrective action in the event of non-compliance. Unfortunately, the Bitcoin Gold (BTG) blockchain was unable to anticipate or prevent this from happening in May 2018, and a similar attack was repeated in January 2020, causing an unknown actor to spend almost $70,000 on BTG.
In all of these cases, the 51% attack was made possible by a single attacker on the network gaining control of more than 50% of the hashing power and then proceeding to perform deep reorganizations of the original blockchain that reversed the transactions. . finished.
The repeated attacks on Bitcoin Gold point to the importance of trusting ASIC miners instead of cheaper GPU-based mining. Since Bitcoin Gold uses the Zhash algorithm which makes mining possible even on consumer graphics cards, attackers can afford to launch a 51% attack on your network without needing to invest heavily in the more expensive ASIC miners.
This 51% attack example highlights the superior security controls offered by ASIC miners, as they require a higher investment to obtain and are designed specifically for a particular blockchain, making them useless for mining or attacking other chains. of blocks.
However, in the event that cryptocurrency miners like BTC switch to smaller altcoins, even a small number of them could potentially control more than 50% of the smaller altcoin network hash rate.
Also, with service providers like NiceHash allowing people to rent hash power for speculative crypto mining, the costs of launching a 51% attack can be dramatically reduced. This has drawn attention to the need to monitor real-time on-chain reorganizations on blockchains to highlight a continuous 51% attack.
MIT Media Lab’s Digital Currency Initiative (DCI) is one such initiative that has created a system to actively monitor a number of PoW blockchains and their cryptocurrencies, reporting any suspicious transactions that may have double-spent the native token. during a 51% attack.
Cryptocurrencies like Hanacoin (HANA), Vertcoin (VTC), Verge (XVG), Expanse (EXP), and Litecoin Cash are just a few examples of blockchain platforms that faced a 51% attack as reported by the DCI initiative.
Of these, the Litecoin Cash attack in July 2019 is a classic example of a 51% attack on a proof-of-stake blockchain, despite the fact that the attackers did not mine any blocks
Resource: cointelegraph